Here is how you install a Go Daddy Certificate on a Cisco ASA for use with AnyConnect. This assumes you already have anyconnect up and running.
1) Open and log into the ASDM.
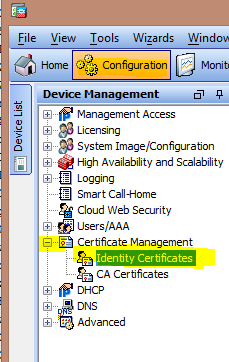
2) Click on "Configuration", "Certificate Management", "Identity Certificates".
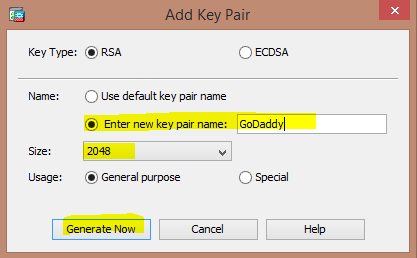
3) Click "Add", Give the Trustpoint a name (for example "GoDaddy"), select "Add a new identity certificate." Click "New", select "Enter new key pair name", and name it. Change the size to 2048 (Go Daddy no longer allows 1024). If you cannot select 2048, you need to update your ASA. Click "Generate Now".
4) Next to "Certificate Subject DN" click "Select".
5) Fill in the Attributes. Don't worry about Location or Email. Then Click "OK"
Common Name- This is the name of the domain URL you will use. For example, vpn.company.com
Department- This is the department in your company, say "IT".
Company Name- Your company name, say "Company"
Country- "US" for United States.
State- Your state, "CO" for Colorado in my example.
6) Click "Add Certificate" and save your CSR somewhere.
7) Go to Go Daddy's site, order your cert and paste your CSR. Once it is issued, download the certificate. Choose "Other" when asked what server type.
8) Go back to identity certificates (see step 1), click on your cert and click "Install".
7) Select the certificate that has a numbered name. DON'T select the one called gd_bundle-g2-g1.crt, that's the intermediate cert. It will be called something like 89438f6489342cc.crt.
8) Open the file gd_bundle-g2-g1.crt, you'll see two certificates with
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
9) Remove the second certificate from the file and paste it into a new file, save the file with a .crt extension. So you'll have two files. The first with the first certificate in the file, the second with he second certificate.
10) Click on "Configuration", open "Certificate Management", click on "CA Certificates." (Your ASDM Certificate should already be located under "Identity Certificates")
11) Click "Add", select your first file, click install certificate. Repeat for the second file. You then should see two files listed.
7) Click "Apply", then "Save".
If you have trouble with step 8, you can download the files from here-
https://www.dropbox.com/sh/ltvx4olrcev7osk/AAAubPLuFXfEoojewaHE9gUIa?dl=0